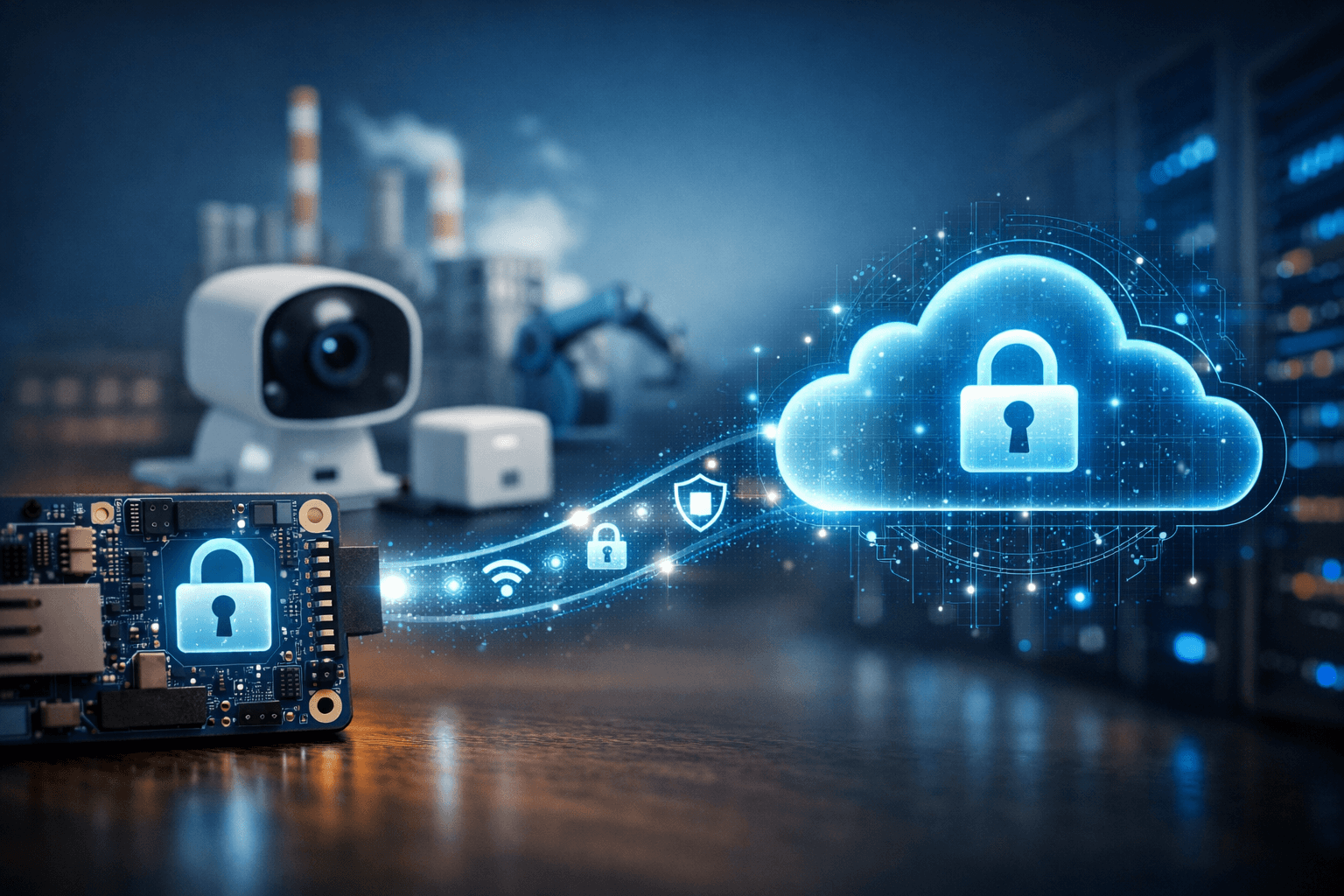
Introduction to Cloud-Connected IoT Devices
Cloud-connected devices sit at the intersection of hardware, software, and distributed systems—and that intersection is exactly where most failures happen.
A cloud-connected IoT device is not just a piece of hardware with internet access. It is a node in a wider system that includes backend infrastructure, data pipelines, security frameworks, and lifecycle management.
The mistake most teams make is treating hardware as the product and the cloud as an add-on. In reality, the cloud is part of the product, and security must be engineered across the entire stack from day one.
IoT adoption is accelerating across industries—industrial automation, healthcare, logistics, and consumer electronics—but so are attacks. Weak devices are now one of the easiest entry points into enterprise systems.
1. Core Architecture of Cloud-Connected Devices
At a high level, every IoT system has three layers:
- Device layer (sensors, actuators, MCU/SoC)
- Connectivity layer (Wi-Fi, cellular, LPWAN)
- Cloud/backend layer (data ingestion, processing, APIs)
Where teams go wrong is not defining clear boundaries between these layers.
Device vs Cloud Responsibilities
Push too much to the cloud → latency, cost, and reliability issues
Push too much to the device → complexity, security exposure, and hardware constraints
The right split depends on:
- Latency tolerance
- Power availability
- Security requirements
- Data volume
Edge vs Cloud Processing
Edge processing reduces bandwidth and improves responsiveness—but increases attack surface.
If your device makes decisions locally, you must assume it will eventually be compromised. Design accordingly.
2. Hardware Design Considerations for IoT
Hardware decisions lock you in early—and undoing them later is expensive or impossible.
Choosing the Right MCU or SoC
Key factors:
- Hardware crypto support (AES, SHA, ECC)
- Secure boot capability
- Trusted execution environment (TEE)
- RAM/Flash headroom for updates
Cheap chips often lack proper security primitives. That “saving” becomes a liability later.
Power Strategy
Battery-powered devices force trade-offs:
- Frequent connections = better security updates but worse battery life
- Deep sleep = longer life but delayed patching
You need to design update cadence into your power model—not bolt it on later.
Memory Constraints
Security features consume memory:
- TLS stacks
- Certificate storage
- OTA update buffers
If you under-spec memory, security becomes the first thing sacrificed. That’s not a technical issue—it’s a business risk.
3. Connectivity Options and Trade-offs
There is no “best” connectivity—only trade-offs.
Wi-Fi
- High bandwidth
- Low cost (infrastructure-dependent)
- Weak in unmanaged environments
Cellular (LTE/5G, NB-IoT)
- Strong coverage
- Higher cost (modules + data plans)
- Better for critical deployments
LPWAN (LoRa, Sigfox)
- Ultra-low power
- Very limited bandwidth
- Requires careful protocol design
Designing for Intermittent Connectivity
Assume:
- Connections will drop
- Packets will be lost
- Devices will go offline for days
Your system must:
- Queue data locally
- Retry safely
- Maintain state integrity
4. Secure Hardware Foundations
This is where most IoT products quietly fail.
Hardware Root of Trust
A root of trust is a secure anchor that verifies everything else:
- Bootloader
- Firmware
- Updates
Without it, your device cannot prove it hasn’t been tampered with.
Secure Elements and TPMs
Dedicated chips (e.g., secure elements) store:
- Private keys
- Certificates
- Cryptographic operations
This prevents key extraction—even if the main MCU is compromised.
If your threat model includes physical access (and it should), this is non-negotiable.
Secure Boot
Secure boot ensures:
- Only signed firmware runs
- No unauthorised code executes
Skip this, and you’ve essentially handed attackers full control.
5. Device Identity and Authentication
Every device must have a unique, verifiable identity.
Identity Provisioning
Options:
- Inject credentials during manufacturing
- Generate keys on-device
The second option is generally safer—but harder to manage.
Certificate-Based Authentication
Using certificates:
- Scales better than shared keys
- Enables revocation
- Supports zero-trust models
Credential Management at Scale
Here’s the reality:
Managing 10 devices is easy
Managing 10,000 devices breaks most systems
Managing 1M devices exposes every shortcut you took
Plan for scale from the start.
6. Data Security: Encryption Strategies
Security isn’t a feature—it’s a baseline.
Encryption in Transit
Use:
- TLS (TCP)
- DTLS (UDP)
Anything less is unacceptable in modern deployments.
Encryption at Rest
Sensitive data stored on devices must be encrypted:
- Logs
- Credentials
- Cached payloads
Key Management
This is the hardest part:
- Where are keys stored?
- How are they rotated?
- What happens if compromised?
If you don’t have answers, you don’t have security—you have assumptions.
7. Firmware and OTA Update Mechanisms
If you cannot update your devices, you do not control them.
Why OTA is Non-Negotiable
Bugs are inevitable
Vulnerabilities are guaranteed
Updates are survival
Secure Updates
Requirements:
- Signed firmware
- Version control
- Rollback protection
Avoiding Bricking
Failed updates kill products and brands.
Design:
- Dual-bank firmware
- Safe rollback paths
- Power-loss resilience
8. Cloud Integration and Backend Design
Your cloud is not just storage—it is your control plane.
Choosing a Cloud Platform
Consider:
- Scalability
- Security tooling
- Device management features
Communication Protocols
- MQTT: lightweight, efficient, IoT standard
- HTTP/REST: simple but heavier
MQTT is usually the better default.
Scaling Securely
At scale:
- Authentication bottlenecks appear
- Latency compounds
- Misconfigurations multiply
Design for millions—even if you start with hundreds.
9. Edge Intelligence and Security Implications
Edge intelligence reduces cloud load—but increases risk.
When to Use Edge Processing
- Real-time decisions
- Bandwidth constraints
- Privacy-sensitive data
Security Trade-offs
More logic on-device =
- More attack surface
- More reverse engineering risk
Encrypt, obfuscate, and assume exposure.
10. Regulatory and Compliance Requirements
Ignore this, and you’ll pay later.
Data Privacy
Regulations like GDPR impact:
- Data storage
- User consent
- Data transfer
Industry Standards
Examples:
- Medical (FDA, MDR)
- Industrial (IEC standards)
Security Certifications
Certifications increase trust—but also cost and timeline.
Plan for them early if your market requires it.
11. Manufacturing and Secure Provisioning
Security doesn’t start in software—it starts in the factory.
Secure Key Injection
Keys must be:
- Unique per device
- Injected securely
- Never exposed in plaintext
Supply Chain Risks
Your weakest link might be:
- A contract manufacturer
- A compromised component
- A rogue insider
Assume the supply chain is hostile.
12. Lifecycle Management of IoT Devices
Shipping the device is the beginning—not the end.
Monitoring and Health
Track:
- Connectivity
- Performance
- Security anomalies
Fleet Management
You need:
- Remote configuration
- Bulk updates
- Segmentation
End-of-Life
Devices don’t just disappear.
You must:
- Revoke credentials
- Disable access
- Handle data securely
13. Common Security Failures in IoT Hardware
Patterns repeat:
- Hardcoded credentials
- No secure boot
- No OTA updates
- Weak encryption
- No threat modelling
These are not edge cases—they are industry norms.
Avoid them, and you already outperform most competitors.
14. Best Practices for Building Secure IoT Hardware
Security-by-Design
Security is not a layer—it is a foundation.
Defence in Depth
Assume failure at every layer:
- Hardware
- Firmware
- Network
- Cloud
Design redundancy into security.
Continuous Testing
Security is not static:
- Penetration testing
- Firmware audits
- Ongoing updates
15. Future Trends in Secure Cloud-Connected Devices
AI-Driven Security
Devices will increasingly:
- Detect anomalies locally
- Respond autonomously
Zero Trust Architectures
Every interaction is verified—no implicit trust.
Emerging Hardware Security
Expect:
- More integrated secure enclaves
- Better hardware-based isolation
- Stronger cryptographic acceleration
Final Takeaway
Most IoT failures aren’t due to lack of innovation—they’re due to ignoring fundamentals.
If you cut corners on:
- Hardware security
- Device identity
- OTA updates
- Cloud architecture
You will pay for it later—in breaches, recalls, or lost customers.
Designing secure cloud-connected devices isn’t about adding features.
It’s about making deliberate, often uncomfortable decisions early—before scale exposes your weaknesses.

0 Comments